Most organizations have limited visibility into personal data due to the large volume of personal data they collect and their spread across heterogeneous systems. Personal data is distributed across many platforms and systems such as on-premises, hybrid, and multi-cloud data assets. Besides, certain types of big data such as logs can be very homogeneous and repetitive. The increasing use of technology has also made the multiplication of data extremely easy and fast. All of this eventually makes it hard for an organization to locate personal data and understand how they should handle it. The data sprawl also increases the risk of privacy and security breaches.
Sensitive Data Intelligence helps organizations overcome these challenges by creating visibility into personal and sensitive data across all organizational structures. This visibility allows organizations to classify datasets as per their sensitivity, assign risk scores to datasets depending on how much security a particular type of dataset needs, and link data to its correct owners (data subjects). All of this is achieved by streamlined workflows and policy-based automation.
Let’s look into some of the reasons why organizations must adopt Sensitive Data Intelligence:
With more than 120 countries having data privacy laws in place and regulations like GDPR and CCPA taking the lead, the legal requirements on protecting personal data are only expected to become stricter with time. No matter where an organization is situated, it is likely to be subject to one to two data privacy laws.
Without knowing what personal data an organization holds, where it is stored, whose data it is, and how they can track it, it is almost impossible for an organization to fulfill its legal requirements as per applicable privacy laws. Sensitive Data Intelligence helps organizations answer all such questions and ultimately ensure compliance with global privacy laws.
A few examples of SDI-driven privacy compliance include the following:
Different data categories can have other privacy and security risks. The more sensitive the data is, the higher the risk of harm on a data subject. Even the breach of a small amount of highly sensitive data can have severe consequences on an individual. Sensitive Data Intelligence enables organizations to understand their data risk profile, identify emerging risk areas promptly and implement necessary controls before data is exposed in case of a security incident. With the help of Sensitive Data Intelligence, an organization is better equipped to choose an appropriate security control relevant to the particular kind of data processing and mitigate any privacy or security risks associated with the data processing.
Without being aware of what and where personal data resides in an organization, they cannot undertake migration of on-premises data to cloud data warehouses and data lakes adequately. Sensitive Data Intelligence helps organizations in an effective and secure cloud data migration journey. SDI assists organizations to discover, analyze, and classify on-premises data. It also detects sensitive data for multi-cloud environments post-migration. Eventually, organizations can apply appropriate security controls across cloud applications.
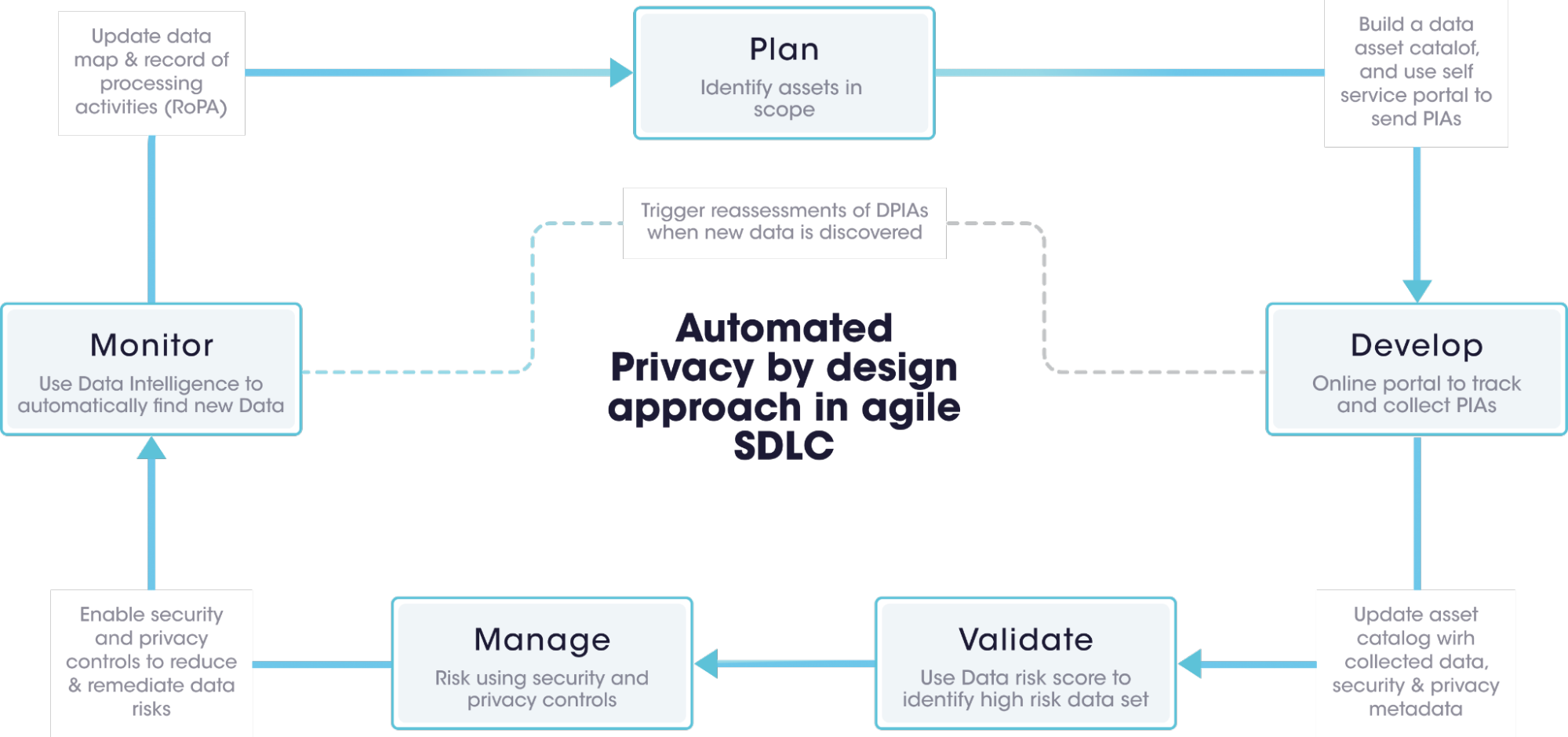
Sensitive Data Intelligence incorporates privacy principles into products and services of all stages of software/product development. Typically, a software-development-life cycle has five stages: planning, development, validation, management, and monitoring. Sensitive Data Intelligence has a role in all these five stages, thereby enabling organizations to embed dynamic assessment processes into SDLC that trigger assessments every time new and sensitive data elements appear in their software products or services. This happens continuously and in an agile fashion.
Sensitive Data Intelligence assists organizations in keeping the personal data only for the period it is necessary for data processing purposes. The periodic scanning of all data assets and visibility into personal data enables organizations to address risks around data storage and comply with data retention policies.
[email protected]
Securiti, Inc.
3155 Olsen Drive
Suite 325
San Jose, CA 95117